Wired
Quantum-Proof Security in a Post-Quantum Era: QKD in Fiber Networks

Key Points
- The emerging quantum computers pose threats to classical cryptography, where data security based on computational complexities of intractable mathematical problems is challenged by Shor’s and Grover’s algorithms. Quantum key distribution (QKD) is a promising solution to key exchange, providing information-theoretic security guaranteed by quantum mechanics.
- CableLabs is a pioneer in innovations that enable quantum/classical data coexistence in a shared fiber and the integration of quantum channels into deployed fiber infrastructures.
- We invite operators, vendors and researchers to collaborate on field trials, standards development and commercialization strategies for this technology.
As fiber networks continue to evolve to meet the demands of next-generation connectivity, a new data security issue has emerged. The security of modern cryptographic systems relies on the computational complexity of intractable mathematical problems, for which it takes an impractically long time to solve using classical computers.
Take two key exchange algorithms as examples. The security of Rivest-Shamir-Adleman (RSA) algorithms relies on the difficulty of factoring a large number into prime factors. The Diffie-Hellman (DH) algorithm is based on the difficulty of the discrete logarithm problem: it's easy to calculate powers but hard to find the exponent. These asymmetric cryptographic (public key) algorithms are widely used for key exchange and authentication in today’s telecommunications. Shor’s algorithm, however, when running on a quantum computer, can solve these math problems, making today’s public-key algorithms vulnerable.
Two strategies address threats posed by quantum computers: post-quantum cryptography (PQC) from a mathematical perspective and quantum key distribution (QKD) from a physics perspective. Before examining the fundamentals of quantum mechanics — and the promise (and challenges) of the quantum internet of tomorrow — it’s worth grounding this discussion in what’s already possible today.
CableLabs is actively advancing practical, deployable approaches to QKD in deployed fiber optic networks, focusing on real-world operator constraints such as cost, scalability and integration with existing classical data traffic. We break down these efforts below, but first we’ll discuss the concepts that provide the technical foundation for understanding why these approaches work — and why they matter for broadband operators preparing for a post-quantum future.
What Are Post-Quantum Cryptography and Quantum Key Distribution?
PQC algorithms exploit the computational complexity of new math problems that even quantum computers struggle to handle, such as lattice-based puzzles and hash-based signatures. Security based on computational complexity is not guaranteed, since it is based on the assumption that there is not enough computational power, or that nobody knows how to solve these problems efficiently. Because computational power is ever growing, problems that cannot be solved today will eventually become solvable. This pattern has been repeated with the Data Encryption Standard (DES), 3DES and RSA algorithms.
The National Institute of Standards and Technology (NIST) has organized several rounds of competitions of PQC algorithms. Two finalists, the post-quantum signature scheme Rainbow and Supersingular Isogeny Key Encapsulation (SIKE), however, were broken on laptops in 2022.
QKD, on the other hand, transmits information via quantum bits (qubits), whose security is guaranteed by quantum mechanics and independent from the computational power of adversaries. Although it faces challenges in real-world deployment, QKD provides absolute security to key exchange and has been adopted in several critical scenarios, such as bank transactions, government elections and defense communications. It’s fascinating that the revolution in quantum technologies plays both a spear and a shield, posing threats and remedies at the same time to today’s telecommunications.
What Is a Qubit, and Why Does It Matter?
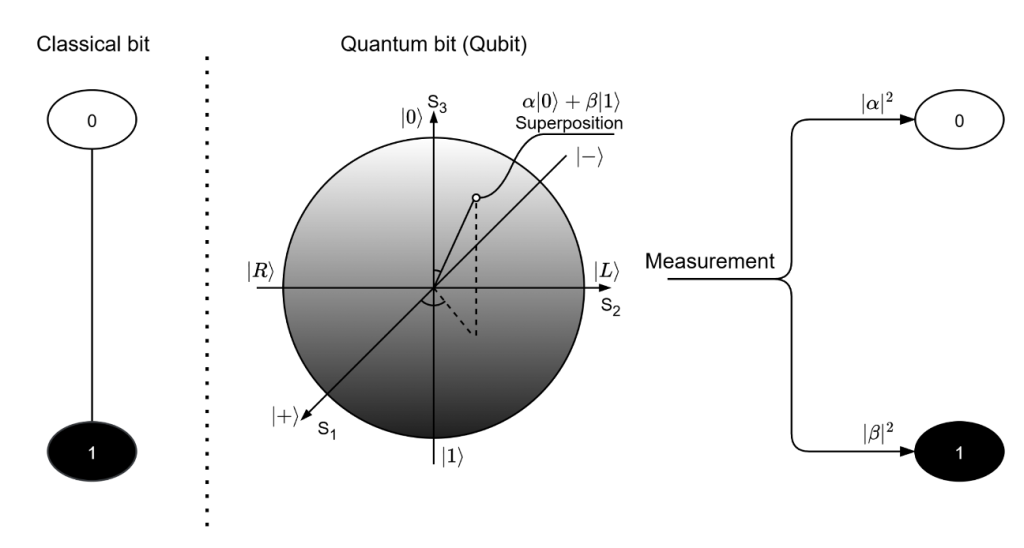
In today’s computers, information is stored using bits, which can be either a 0 or a 1. A qubit — the quantum version of a bit — can hold something much richer. Thanks to the rules of quantum mechanics, a qubit can be in a state that represents both 0 and 1 at the same time. This property is called superposition.
A simple way to picture this is with colors:
- A classical bit is like choosing black or white.
- A qubit can be any shade of gray between the two, representing a blend of 0 and 1 (Figure 1).
When we eventually measure a qubit, it “collapses” to either 0 or 1. The shade of gray tells us the probability of getting each outcome. Here, it is not the state (color), but the portions or probabilities of each state that carry the information of a qubit. This is a fundamental deviation from classical bits.
Superposition, the ability to hold many possible states at once, is what gives quantum technology its potential power — allowing more information to be carried and more complex operations to be performed than with classical bits.
Quantum mechanics also brings built‑in security benefits.
- A qubit is carried by a single photon — a particle that can’t be split.
- Due to the no-cloning theorem, an unknown qubit can’t be copied perfectly. An unknown qubit can only be measured correctly using the basis in which it was prepared; otherwise, the measurement leads to random results, changes the state of the qubit and reveals the presence of an eavesdropper.
Quantum mechanics offers something classical systems cannot: built‑in protection against copying or eavesdropping. This is why qubits are exploited in QKD, which can detect interception attempts automatically.
Figure 1. Classical bit and quantum bit (qubit).
In a QKD system, a sender — referred to as Alice in cryptography scenarios like this — sends a sequence of qubits to a receiver (known as Bob). Due to the channel loss and lack of amplification, most qubits are lost on the way; only a small portion arrives at Bob. Since the photons that arrive at Bob are secure (i.e., not divided, copied or measured along the way), these qubits can be used to establish a confidential key between Alice and Bob without information leakage.
If an eavesdropper (Eve) performs an intercept-resend attack, since she does not know the basis Alice used to prepare the qubit, there is a good chance she uses a wrong basis and gets random results, revealing no information to Eve. Also, if Eve uses a wrong basis, the qubit she duplicates and sends to Bob will differ from the original one, so Alice and Bob can tell their communication has been tapped. They can exploit privacy amplification protocols to eliminate the information Eve stole and extract secure keys only from those qubits that are not tapped. If too many qubits are tapped, Eve might have stolen too much information. Alice and Bob would abort all keys and restart the QKD operation. QKD acts like an alarm system, alerting the sender and receiver if the transmitted qubits are tampered with.
Another foundational concept in quantum mechanics is entanglement — a special connection between two photons where their states are linked. Even when separated, the measurement results of entangled photons are correlated. If one photon collapses to 0, the other instantly collapses to a matching or complementary state, depending on how the entangled pair was prepared.
Entanglement isn’t just a scientific curiosity. It enables:
- More advanced QKD schemes
- Quantum teleportation of information
- Early forms of a quantum internet, where quantum states can be shared across networks of quantum devices
It’s a powerful resource for long‑distance, ultra‑secure communication.
Real-World Impact: Field Trials and Use Cases
QKD is rapidly transitioning from the lab into real networks, especially where confidentiality is mission‑critical. Early adopters include government and defense agencies securing diplomatic and intelligence traffic, often in combination with post‑quantum cryptography. Major telecom operators — such as Verizon, Deutsche Telekom, Orange, BT, DoCoMo and SK Telecom — are running pilots to integrate QKD into their backbone and metro networks. Banks like JP Morgan are exploring QKD to protect data‑center links, while health care and critical‑infrastructure operators are evaluating it to safeguard sensitive clinical and industrial‑control data.
Quantum key distribution (QKD) can be transmitted over terrestrial optical fibers, free-space links in the atmosphere, or between satellites in space. China’s 2016 Micius satellite demonstrated intercontinental QKD over 7,600 km, inspiring similar efforts such as Canada’s QEYSSat and Europe’s Space QUEST. Satellites provide long‑distance, low‑latency links, though they face challenges such as high launch costs, limited nighttime communication windows and weather sensitivity.
Despite these advances, optical fiber remains the most widely deployed medium due to its low cost and availability. Since the DARPA quantum network in Boston (2004), many metro‑scale QKD networks have been built in cities such as Geneva, Vienna, Tokyo and Cambridge. China has also deployed the first long-haul QKD network from Beijing to Shanghai over 2,000 km, using trusted nodes to span the long distance.
Standards efforts are maturing as well. ISO/IEC has established the first global QKD evaluation standard, covering security assurance and interoperability. ETSI is defining system architectures, interfaces, key‑management protocols and hybrid operation with PQC. Leading QKD vendors include ID Quantique (Switzerland), Toshiba (Japan), QuantumCTek (China), Fraunhofer HHI (Germany), QTI (Italy) and LuxQuanta (Spain).
How Does QKD Compare to PQC?
Relying on fundamental laws of quantum mechanics, QKD offers information-theoretic security that PQC cannot. But it cannot replace all cryptographic algorithms or address all security issues in the post-quantum era.
Modern data security includes three key aspects: authentication, key exchange and encryption/decryption, as shown in Table 1 (below). Asymmetric cryptographic algorithms, such as RSA and Diffie-Hellman, which are used for authentication and key exchange, are vulnerable to Shor’s algorithm running on a quantum computer. Symmetric cryptographic algorithms, such as the Advanced Encryption Standard (AES), used for data encryption and decryption, are considered safe against quantum computers. Although Grover’s algorithm on a quantum computer can weaken symmetric algorithms, the symmetric algorithms are still regarded as quantum safe as long as sufficiently long keys are used (for example, AES256).
QKD provides absolute security for keys in flight — or data in transit — during the key exchange, whereas authentication will still rely on PQC algorithms. Moreover, specialized hardware, direct fiber connections and high deployment costs have hindered QKD from widespread commercial adoption.
Although PQC cannot offer the same theoretical perfect security as QKD does, PQC algorithms are far more practical to deploy widely as they are fast, inexpensive and versatile. They can be deployed directly in existing networks via software upgrades, without hardware modifications, making them a cost-effective option for addressing short-term threats from quantum computing. This is why Microsoft and other companies prioritize PQC as the primary defense against quantum threats.
Table 1. Three aspects of modern data security
| Aspect | Legacy Defense | Vulnerability to Quantum Computers | Quantum-Proof Defense |
|---|---|---|---|
| Authentication | Asymmetric crypto algorithms | Yes | PQC |
| Key exchange | Asymmetric crypto algorithms | Yes | QKD or PQC |
| Encryption | Symmetric crypto algorithms | Weakened; still safe if sufficiently long keys are used | AES-256 |
In the long term, a hybrid system combining QKD and PQC that operates in a coordinated, complementary manner would provide the highest security in the post-quantum era. A hybrid system with QKD for key exchange, PQC for authentication and AES for encryption will soon be applied in critical communications, such as government, defense and financial networks, where the primary security considerations justify the high cost and complexity of QKD systems.
Meanwhile, many commercial and residential networks will rely on PQC to provide short-term security.
Table 2 compares QKD and PQC.
Table 2. QKD vs PQC
| Aspect | Quantum Key Distribution (QKD) | Post-Quantum Cryptography (PQC) | Legacy Cryptography |
|---|---|---|---|
| Security | Quantum mechanics | New math problems — lattice, hash, code, multivariate crypto | Old math problems — RSA (large number factorization), Diffie-Hellman (discrete logarithm), AES |
| Defense model | Detect qubit tapping during key exchange | Difficult to decrypt by classical and quantum computers | Difficult to decrypt by classical computers |
| Implementation | Quantum hardware, optical links, expensive to install and maintain | Software only, no hardware upgrade, low cost | |
| Scalability | Mostly point-to-point links, ~100 km distance, Mb/s key rate | High scalability | |
| Standardization | ISO/IEC 23837, ETSI QKD 014 | NIST | Done |
| Application | Critical communications only — government, defense, financial | Short-term commercial | Everywhere |
Overcoming Challenges and Looking Ahead
Although quantum technologies offer immense promise, several challenges still hinder their commercial deployment, including distance limitations, noise sensitivity and integration with passive optical networks (PONs).
Distance Limit
For a channel with 10 dB of loss, a classical signal is 10 times smaller after propagation, and this loss can be compensated for by amplification. In quantum communication, only 1 out of 10 qubits will arrive at the receiver, and no amplification is allowed due to the no-cloning theorem. The achievable key rate depends on the number of qubits arriving at the receiver, so the key rate scales linearly with the channel transmittance. Since fiber transmittance decays exponentially with distance, all QKD protocols must make a tradeoff between key rate and distance, as key rates drop exponentially with distance. Most QKD systems are limited to Mb/s key rates or ~100 km distance, and these limits cannot be achieved simultaneously.
Coexistence with Classical Data
A quantum signal has less than one photon per pulse, whereas a classical signal has one to ten million photons per pulse. The spontaneous Raman scattering (SpRS) noise from strong classical data traffic can easily overwhelm a QKD system, making the reception of single photons impossible.
To alleviate the noise from classical traffic, most commercial quantum systems require dedicated or dark fibers. This is not a good idea from a deployment perspective, since fibers are scarce and expensive resources. It is cost-prohibitive and impractical to add or dedicate fiber for quantum-only purposes, especially in cost-limited, fiber-deficient access networks. The only chance for the commercial success of quantum technologies is integration into existing fiber infrastructure and sharing the deployed fibers with ongoing classical traffic, which, in turn, raises the problem: how to mitigate SpRS noise from classical communications.
Integration Into PONs
Although many QKD systems have been deployed in long-haul and metropolitan networks, very few QKD systems have been deployed in PONs to deliver quantum keys to end users. As the last mile of fiber networks, PONs are not only the bottleneck of data throughput but also the most vulnerable segment for data security, where eavesdropping exploits the point-to-multipoint (P2MP) topology and downstream data broadcasting to all users.
Although fiber distance is no longer an issue in access networks, since most PONs are less than 50 km, fiber deficiency and stringent cost constraints force QKD links to be integrated into PONs and to share the only fiber with existing data traffic, where the SpRS noise from downstream and upstream data becomes problematic.
CableLabs is tackling these challenges with pioneering approaches:
- Coexistence strategy in point-to-point networks. CableLabs has demonstrated a novel time-interleaving technique to separate quantum and classical channels in both time and spectrum domains, so that quantum and classical data traffic can share the same fiber while isolating the SpRS noise.
- QKD in next-generation PONs. CableLabs demonstrated a new wavelength multiplexing method to integrate QKD into next-generation PONs, including coherent PON and NG-PON2, without adding fibers or modifying deployed PON infrastructures.
With these innovations, the broadband industry now has a unique opportunity to embed quantum technologies into its fiber networks, enabling not only quantum-proof data security but also future-proof quantum interconnect for the upcoming quantum internet. The innovations developed at CableLabs allow the integration of quantum links into deployed fiber networks at low cost.
Join the Quantum Revolution
The quantum revolution aligns with quantum-proof data security and the quantum internet outlined in the CableLabs Technology Vision, positioning broadband networks as a unique and foundational platform for both.
Quantum is more than a technical innovation; it’s a strategic asset for cable operators. By integrating quantum capabilities into their fiber networks, operators can leverage their extensive fiber deployments to provide quantum-safe security and also create ubiquitous connectivity for the emerging quantum internet.
To learn more about our work in quantum technologies, check out these recent papers published by IEEE and the Institution of Engineering and Technology:
- Integration of Quantum Key Distribution in a 20-km 32-user Coherent Passive Optical Network with Single Feeder Fiber
- Time-interleaving enabled co-propagation of QKD with a 10-dBm 100-Gb/s QPSK channel over 100-km fiber
- Time-Interleaved C-Band Co-Propagation of Quantum and Classical Channels
We invite operators, vendors and researchers to collaborate on field trials, standards development and commercialization strategies. Whether you're exploring QKD and entanglement or integrating quantum technologies into your network, now is the time to engage. Reach out to us, Dr. Steve Jia and Dr. Jing Wang, to get started.